HIPAA Compliance and Attestation Support
Improve your business’ Protected Health Information (PHI) security by being HIPAA compliant.
Our tailored services are designed to ensure that your organisation meets the stringent requirements of the Health Insurance Portability and Accountability Act (HIPAA)
We work with the auditors and provide ongoing support to help manage and maintain HIPAA compliance to address any evolving regulatory needs.
We work with amazing customers



We are a team of experienced cybersecurity specialists on a mission to get you HIPAA compliant.
At AMARU, we specialise in assisting Australia and New Zealand businesses through the HIPAA compliance journey and collaborate with auditors to get you HIPAA compliant in no time! Our comprehensive services are designed to streamline the compliance process and ensure a successful outcome for your business.
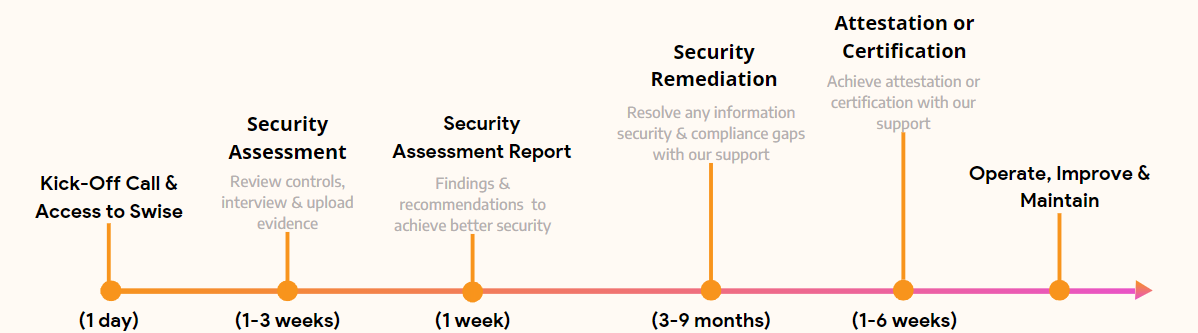
HOW IT WORKS
How can being HIPAA compliant help businesses?
By being HIPAA compliant, Australia and New Zealand businesses can demonstrate a high standard of IT security standards and prevent risks that can compromise patient data.
Robust Data Security
Achieving HIPAA compliance enhances data security, instilling trust and confidence in your organization’s ability to protect sensitive healthcare information.
Regulatory Adherence
By obtaining HIPAA certification, your organisation demonstrates a commitment to upholding the regulatory standards set forth by HIPAA, mitigating the risk of non-compliance penalties.
Industry Recognition
Businesses across Australia and New Zealand region can stand out in the healthcare industry by showcasing your dedication to maintaining the highest standards of data privacy and security.

Kickstart your HIPAA compliance journey with AMARU
Our team of experienced professionals provide expert guidance and support throughout the HIPAA compliance journey, ensuring a smooth and efficient process.
We understand that every business is unique, which is why we offer tailored solutions to address your specific compliance needs and requirements.
Beyond the certification and attestation process, we provide ongoing support to help your business maintain HIPAA compliance and address any evolving security needs.
Case Study
Oceania is New Zealand’s premium retirement living and aged care provider. They have 3000 staff and 4000 residents spread across 43 sites over the country.
With cyber security incidents continuously featuring in news headlines, the board at Oceania wanted confidence that they were prepared for a cyber security incident. They approached AMARU, who they knew to be pragmatic, solution focused experts in their field, to deliver a cyber security incident response plan.
Frequently Asked Questions
See our frequently asked cyber security questions below for help and advice.
Why is being HIPAA compliant important for my organisation?
HIPAA compliance refers to the adherence to the Health Insurance Portability and Accountability Act (HIPAA) regulations, which are designed to protect sensitive patient health information. It is essential for healthcare organisations, as it demonstrates a commitment to safeguarding patient data, avoiding costly penalties, and maintaining trust with patients.
Who needs to be HIPAA compliant?
There are 3 groups that must be HIPAA compliant:
- Covered Entities,
- Business Associates, and
- Business Associate Subcontractors
All of these groups handle PHI on a regular basis and must be equipped to safeguard this sensitive information, though not mandatory for them to get compliant unless your business operates in North America.
Covered Entities are defined as healthcare providers, health plans, and healthcare clearinghouses. Business Associates are the providers that support Covered Entities, usually IT, lawyers, third party administrators, etc. Business Associate Subcontractors are groups that support Business Associates. For example, a physician practice has hired an IT provider and the IT provider bundles services for the practice. In order to do this, the IT provider will contract with a 3rd party for things like cloud backups. In this case, the Physician would have a BA Agreement with the IT provider, and the IT provider would have BA Subcontractor agreements with their 3rd parties.
Does AMARU offer support after getting HIPAA compliant?
AMARU provides ongoing support for Australia and New Zealand businesses that wish to continue maintaining and improving the HIPAA compliance, ensuring long-term adherence to evolving regulations and best practices and ultimately ensure protection of patient data.